ASU’s Next-Gen Cybersecurity event elevates student voices for a conversation on digital trust
“At the root of cybersecurity is trust.”
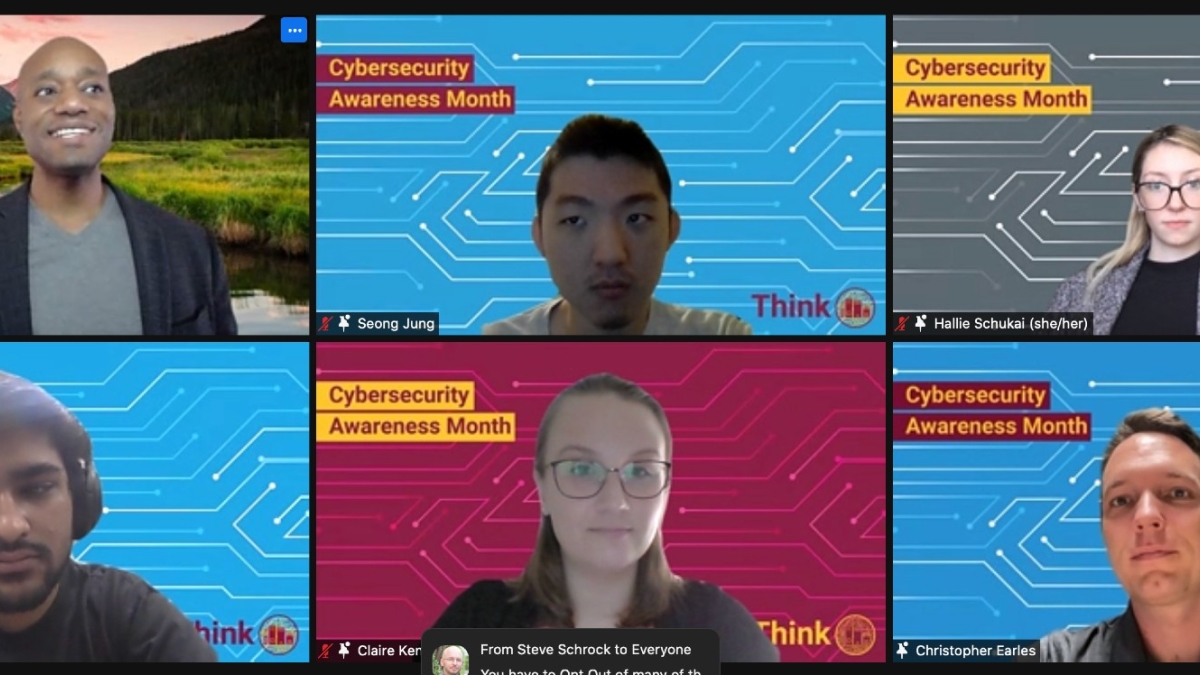
That powerful summary statement came from Hallie Schukai, an Arizona State University junior majoring in computer science. Her insights — along with the ideas, trends and tips surfaced by fellow student panelists — were shared at the University Technology Office’s (UTO) Next-Gen Cybersecurity event, a kickoff for ASU’s Think! Campaign during October’s Cybersecurity Awareness Month.
The central theme that emerged was the importance of digital trust — the background of confidence that users have in their place and security in a virtual world — in the field of cybersecurity.
Rethinking the meaning of cybersecurity
ASU Chief Information Security and Digital Trust Officer Donna Kidwell led the conversation during the event, setting the stage for the perspective of keynote speaker Michael Palmer, chief information security officer at Hearst. His advice in the context of building trust laid the groundwork for conversations to come.
“I'd say the most important thing for me is building relationships,” Palmer said. “The other thing I would (advise) is really trying to be a good storyteller.”
The five-student panel, moderated by UTO Executive Director of Digital Trust Initiatives Timothy Summers, expressed the importance of telling one’s story.
To start, the students offered their insight into the general perception of cybersecurity, since a true sense of what the field entails is a key foundation to any education on the topic.
“I thought cybersecurity was solely about hacking,” Schukai said, explaining that the reputation of cybersecurity has become extreme, depicted in an often “scary” way in the media.

ASU Chief Information Security and Digital Trust Officer Donna Kidwell.
“But a lot of people don’t think much about cybersecurity because they don’t think they’re worth targeting,” said Christopher Earles, who majors in computer science with a focus in cybersecurity.
This reveals a problem with equity, or a level playing field for a diverse set of people, in cybersecurity impact.
“I used to think equity was present in the indiscriminate way people attack,” Earles said.
But his perspective changed when he saw particular demographics targeted in different ways.
Schukai added that many groups, such as the elderly and low-income people with little access to internet information, are particularly affected by phishing scams, which use fake links that appear to be legitimate communications from organizations like the IRS.
Building digital trust
So what are the ways in which these risks can be mitigated? Or as Schukai put it: “How can we log into Facebook or social media with trust in that link going to the verified website?”
“Transparency and trust are really valuable,” said Seong Jung, a junior majoring in applied computing with a focus in cybersecurity. Jung described a three-step approach that companies or institutions take only some or none of: They need to communicate security concerns, devise solutions and implement them.
From that organization side, transparency in data collection is also important.
“When we sign terms and conditions and read them, what do they actually say?” asked Claire Kenison, a major in business data analytics. “All these free services are not really free,” Kenison added, explaining that the selling and use of data is one of the defining problems in cybersecurity.
Individuals can also take steps to protect their information from attackers.
“I need to shout out that there’s free access to LastPass for everyone (at ASU),” said Harsh Tekwani, a junior majoring in computer information systems and business data analytics.
LastPass, a tool that manages passwords, was one of the recommendations for solid cybersecurity practices from the students. Another was the use of browsers with extensive security features; Schukai uses DuckDuckGo; Jung, Firefox.
Kenison also pointed out that many services let you log in to other sites or apps with the same information, so keeping them separate can remove the risk of a chain reaction of breaches. Earles supported that concept by saying it’s not a good idea to use the same password for everything.
Educating everyone on the value of cybersecurity
All of these ideas can cohere into the support of digital trust. Equity, organizational transparency and individual best practices, as identified by these students, are central to it.
Going forward, education can help us achieve these goals.
“Consider who’s most vulnerable to these kinds of attacks,” Jung said, giving a call to action to his cybersecurity-oriented audience to have conversations with vulnerable groups about protecting their information.
Schukai gave a positive outlook to the future of cybersecurity, which often can be talked about in scary, negative terms: “Faith in good people, good organizations and good motivations keep it all spinning!”
Watch the student panel discussion
Check out the fireside chat with Donna Kidwell and Michael Palmer
More Science and technology

Hack like you 'meme' it
What do pepperoni pizza, cat memes and an online dojo have in common?It turns out, these are all essential elements of a great…

ASU professor breeds new tomato variety, the 'Desert Dew'
In an era defined by climate volatility and resource scarcity, researchers are developing crops that can survive — and thrive —…

Science meets play: ASU researcher makes developmental science hands-on for families
On a Friday morning at the Edna Vihel Arts Center in Tempe, toddlers dip paint brushes into bright colors, decorating paper…

